In the last chapter, we delved into the depths of GNU/Linux, exploring user management, file system organization, and basic environment configuration. We learned about the importance of the root user, user and group management, and the hierarchical structure of the file system. These concepts are fundamental to understanding how Linux works and preparing for more advanced tasks.
In this chapter, we will dive deeper into managing file and directory permissions, a crucial aspect of maintaining security
and control in a multi-user system like GNU/Linux. Additionally, we will cover the use of umask to define default permissions
for new files and directories, providing a solid foundation for any user or system administrator.
Understanding the Permission System in Linux
Files in Linux have associated permissions that control who can read, write, or execute them. As with any modern operating system where multiple users can access the same resources, it’s important to have a control system to determine which users can do what with the files. GNU/Linux is no exception, focusing on three categories:
- User (u): The file owner.
- Group (g): The users who are part of the group the file belongs to.
- Others (o): All other users.
To view the permissions of a file, you can use the ls -l command:
ls -l file.txt
The output of this command will look something like:
drwxr-xr-x 2 user group 4096 mar 10 12:34 .
drwxr-xr-x 4 user group 4096 mar 10 12:30 ..
-rw-r--r-- 1 user group 220 mar 10 12:34 .bash_logout
-rw-r--r-- 1 user group 3771 mar 10 12:34 .bashrc
-rw-r--r-- 1 user group 807 mar 10 12:34 .profile
-rwxr-xr-x 1 user group 98 mar 10 12:34 script.sh
The first group of characters is the permissions, starting with the file type (d for directory, - for regular file, and l for symbolic link). The next three characters indicate the owner’s permissions, the next three are for the group, and the last trio are the permissions for others. In the first case “drwxr-xr-x”, the owner can read, write, and execute, the group and others can read and execute. The breakdown is as follows:
- r: Allows reading the file’s contents.
- w: Allows modifying the file’s contents.
- x: Allows executing the file if it’s a script or binary.
Along with the permissions, you can also see the file owner and the group it belongs to, along with other relevant information that is not currently of interest. Permissions in Linux have a numerical (octal) equivalent, which can be seen below:
- r (Read): 4
- w (Write): 2
- x (Execute): 1
- - (No permission): 0
To find out the numeric permissions of a file, you can use the stat command:
stat file.txt
The output will show something like this:
File: file.txt
Size: 6610 Blocks: 16 I/O Block: 4096 regular file
Device: 252,0 Inode: 31101793 Links: 1
Access: (0664/-rw-rw-r--) Uid: ( 1001/betazetadev) Gid: ( 1001/betazetadev)
Access: 2024-05-27 15:58:21.474596420 +0200
Modify: 2024-05-27 15:58:21.475596402 +0200
Change: 2024-05-27 15:58:21.476596383 +0200
Birth: 2024-05-27 15:58:21.474596420 +0200
We can observe that the file access permissions are 0664 (the “0” indicates it is an octal number), which means the owner
and the group can read and write, while others can only read. This is equivalent to rw-rw-r--, so according to this, we
know that the maximum octal number is 7 (4+2+1), so the maximum value that can be assigned is 777, which would be equivalent
to rwxrwxrwx, the least restrictive option in terms of permissions as it allows everything for all users.
The most restrictive permission would be 0, which would not allow the assigned user type to do anything. For example, if 000 is assigned to a file, neither the owner, the group, nor others could do anything with it. This might not make much sense, but it can be done.
It is important to note that improper management of permissions can lead to security issues, so it is important to understand the security requirements of each file and directory in our system, especially those containing sensitive or important information. It is rarely necessary to make files available to all users.
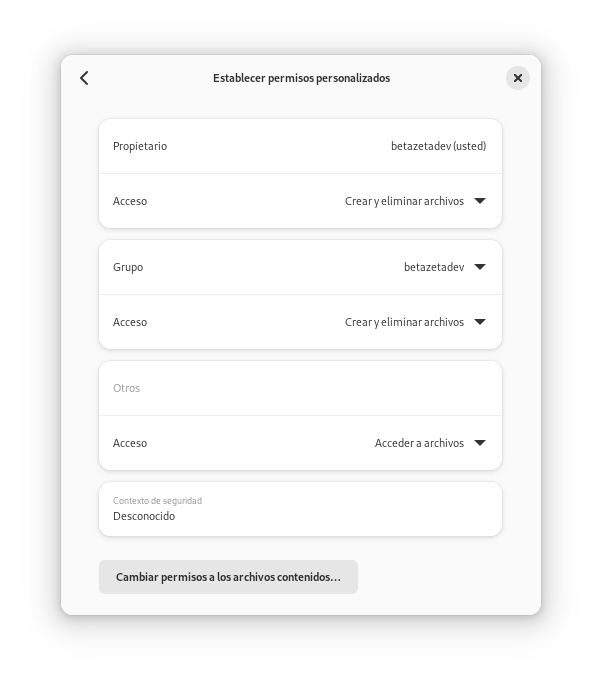
There are different ways to manage files in a GNU/Linux system. Although it can also be done through a graphical interface easily using a file explorer, the most flexible way is through the terminal. Additionally, knowing how they work and being able to change them directly from the terminal allows for maintenance and/or repair tasks to be done more quickly without having to open a program. Often in Linux, work is done on servers without a graphical interface.
To change the permissions of a file, you can use the chmod command:
chmod u+x script.sh # Adds execute permission for the owner
chmod g+w file.txt # Adds write permission for the group
chmod o-r file.txt # Removes read permission for others
chmod a=r filefile.txt # Sets read-only permissions for everyone
We can also use octal notation to change the permissions of a file:
chmod 755 script.sh # Sets read, write, and execute permissions for the owner, and read and execute permissions for the group and others
chmod 700 script.sh # Sets read, write, and execute permissions for the owner, without permissions for the group and others
chmod 664 file.txt # Sets read and write permissions for the owner and group, and read permissions for others
chmod 640 file.txt # Sets read and write permissions for the owner, and read permissions for the group, without permissions for others
chmod 444 file.txt # Sets read-only permissions for the owner, group, and others
This way, we can efficiently manage each and every file in our system. Although it is not the only tool we have at our disposal
to manage file permissions, chmod is one of the most important and widely used. With the chown tool, we can change the
owner of a file:
sudo chown new_owner file.txt
And with chgrp, we can change the group of a file:
sudo chgrp new_group file.txt
The combination of these commands allows us to have complete control over the files in our system, being able to assign custom permissions to each of them, and change the owner and group they belong to. It is important to note that some system files should not be modified, as changing their permissions can cause problems. Additionally, as mentioned earlier, improper management of permissions can lead to security issues, so it is important to understand the security requirements of each file and directory in our system and services.
What is umask and How to Use It
Another important concept in managing permissions in Linux is umask, a value that is subtracted from the default permissions
of files and directories created by a user. Generally, in systems like Ubuntu, the default umask is 0002, which means write
permission for other users is subtracted. In other words, umask determines the default permissions that will be assigned
to new files and directories by subtracting its value from 666 for files and 777 for directories. We can check the current
value with the umask command:
umask
The output will show the current value of umask:
0002
Knowing that the default permissions for files and directories in Linux are 666 (rw-rw-rw-) and 777 (rwxrwxrwx), respectively,
we can calculate the final permissions by subtracting the umask value from these values. For example, a umask of 0002 will
remove the write permission for other users:
- Files: 666 - 002 = 664 (rw-rw-r–)
- Directories: 777 - 002 = 775 (rwxrwxr-x)
This ensures that the files and directories created are accessible by the owner and the group, but not modifiable by other
users. To change the umask value, you can use the umask command followed by the desired value:
umask 0022
This change will apply to all files and directories created from that moment on, although it is usually not necessary to change it since the default value is the most secure and most used in most systems, it may be needed in very specific environments.
Managing permissions in Linux is a fundamental skill for any system administrator or advanced user. From setting basic permissions
with chmod, to adjusting owners and groups with chown and chgrp, and defining default permissions with umask, these
skills will allow you to have complete control over the files and directories in your system. Proper management of permissions
not only guarantees security but also facilitates collaboration and system maintenance.
By mastering these concepts, you will be better prepared to manage and protect your Linux environment, ensuring that resources are correctly assigned and accessible only to those with the appropriate permissions. Moreover, managing them from a graphical interface will be a piece of cake once you understand their internal workings. In the next chapter, we will explore process and system resource management efficiently. See you next time!